6 mins read
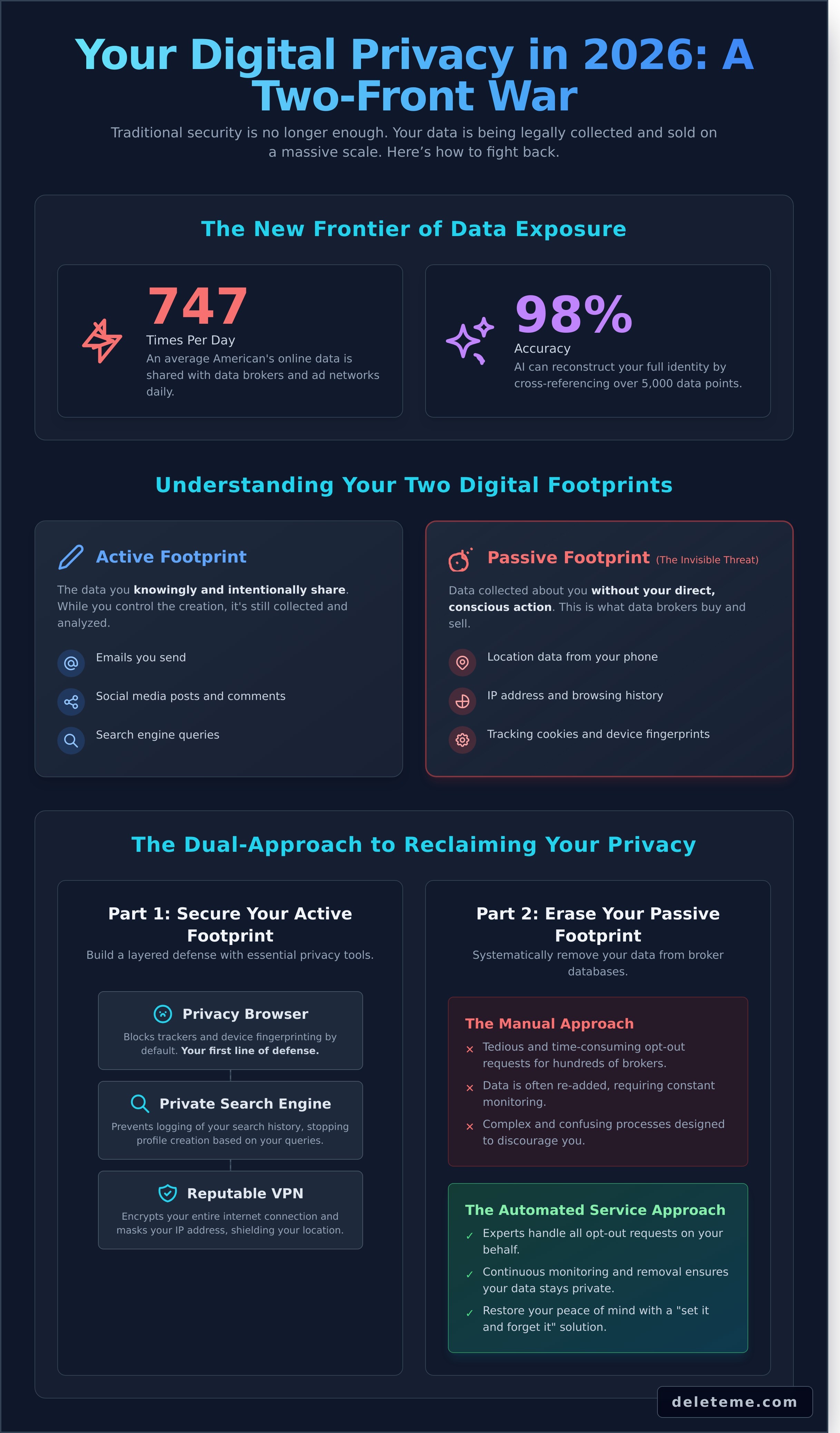
A 2023 report from the Irish Council for Civil Liberties revealed a startling fact: the average American’s online data is shared 747 times every single day. It’s no wonder your phone rings with unknown numbers and ads for a product you just thought about appear in your feed. The feeling that your personal information is no longer your own is a heavy burden, and the complexity of privacy settings often feels designed to make you give up.
But true control isn't out of reach. This definitive 2026 guide will show you exactly how to protect your privacy online by mastering a powerful dual approach: securing your active digital habits while systematically erasing the passive data footprint that data brokers have already collected. We will walk you through the precise steps to lock down your accounts, opt out of invasive tracking, and get your personal information removed from the source, restoring your peace of mind.
Key Takeaways
Discover why traditional security is no longer enough and how AI-powered data aggregation in 2026 requires a new, two-part privacy strategy.
Implement the hierarchy of essential privacy tools-from browsers to VPNs-and learn why end-to-end encryption is the non-negotiable standard for communication.
Learn a step-by-step framework for how to protect your privacy online by auditing your public exposure and systematically removing your data from brokers.
Evaluate the difference between tedious manual opt-out requests and an automated service that uses experts to manage your data removal continuously.
The State of Digital Privacy in 2026: Why Security Isn’t Enough
In 2026, understanding digital privacy is no longer optional. It’s a fundamental aspect of personal autonomy. Digital privacy is your right to control how your personal information is collected, shared, and used by corporations and governments. This concept, central to the broader field of Internet privacy, is often confused with digital security. Security protects your data from unauthorized access, like a hacker stealing your password. Privacy, however, protects your data from authorized, legal exploitation by the companies you interact with every day.
The challenge has evolved. Old advice focused on firewalls and strong passwords, but that addresses only half the threat. The real battle for privacy is now fought against automated systems that legally aggregate vast amounts of your data. The simple tracking cookies of the 2010s have been replaced by AI-powered predictive models that don't just know what you bought; they predict what you'll do, think, and believe next. This is the new frontier of data exposure.
The Rise of AI-Driven Data Scraping
Modern AI tools have fundamentally changed the data landscape. By 2026, advanced algorithms can cross-reference over 5,000 seemingly anonymous data points to reconstruct your full identity with 98% accuracy. Information that once took months to compile, such as linking a public property record to a social media comment and a vehicle registration, now happens in less than a second. This is why traditional privacy tools like your browser's "incognito" mode are obsolete; they only hide your local search history, doing nothing to stop your internet provider, search engines, or the websites you visit from tracking and profiling you.
Active vs. Passive Digital Footprints
An essential first step in learning how to protect your privacy online is understanding the two types of data trails you leave behind. Your digital footprint is composed of both active and passive data, and both are equally valuable to data brokers.
Active Footprint: This is the data you knowingly and intentionally share. It includes your social media posts, the search terms you type into Google, the emails you send, and the online reviews you write.
Passive Footprint: This is the data collected about you without your direct action. It includes your IP address, location data pinged from your phone, your browsing history tracked by cookies, and the profiles data brokers build and sell about you.
In the past, managing your active footprint was sufficient. Today, your passive footprint often reveals more about you than your intentional posts. True digital hygiene in 2026 requires a strategy that actively monitors and manages both of these data trails simultaneously. It requires a guardian, not just a gate. And that's where a service like deleteme becomes essential for your peace of mind.
Securing Your Active Footprint: Essential Tools and Habits
Your active digital footprint is the trail of data you intentionally create every day through browsing, searching, and communicating. Securing it is the first line of defense. A layered approach, using a hierarchy of privacy tools, provides the strongest protection against tracking and data collection. Understanding these tools is a critical step in learning how to protect your privacy online. This isn't about becoming invisible; it's about taking deliberate control over what you share.
The foundation of your defense is your browser, followed by your search engine, and finally shielded by a Virtual Private Network (VPN). Each layer serves a distinct purpose:
Privacy-First Browsers: Tools like Brave or LibreWolf actively block trackers and ads by default. They are designed to combat advanced device fingerprinting, a method used by over 80% of websites as of 2024 to identify you even without cookies.
Private Search Engines: Moving away from Google is essential for data autonomy. Search engines like DuckDuckGo or Startpage don't log your search history, preventing the creation of a detailed personal profile based on your queries.
Reputable VPNs: A VPN encrypts your internet connection and masks your IP address. This is non-negotiable for using public Wi-Fi, as it prevents snooping on unsecured networks and shields your location from the websites you visit.
Privacy-First Browsing and Searching
By 2026, trackers will rely heavily on advanced fingerprinting that analyzes your unique browser and device configuration. A privacy-focused browser is built to resist this by design. For an added layer of security, extensions like uBlock Origin can be configured to block invasive scripts and cross-site tracking elements, which a 2025 CyLab report found on 91% of commercial websites. This combination severely limits the data available to advertisers and data brokers.
Communication and Identity Masking
For all communication, end-to-end encryption (E2EE) must be the standard. This ensures only you and the recipient can read your messages. Services like Signal for messaging or Proton for email provide E2EE by default. Beyond communication, masking your identity during transactions is vital. Using email aliasing services like SimpleLogin prevents your real email from being exposed in data breaches, while virtual credit cards create single-use card numbers to protect your financial information from compromised merchants.
Beyond tools, consistent habits are what sustain your privacy. This means conducting regular "privacy hygiene" audits. At least twice a year, review the privacy settings on your social media accounts, restricting audience settings and deleting old, unnecessary posts. Scrutinize the permissions granted to your mobile apps; a 2025 study from the International Computer Science Institute found that 68% of popular Android apps request at least one "dangerous permission" they don't need to function. Performing these audits aligns with the proactive stance recommended by the FTC privacy and security guidelines, which emphasize minimizing data collection. This consistent maintenance is fundamental to how to protect your privacy online for the long term.
While managing your active footprint is a powerful step, it's only half the battle. Your passive footprint, the data collected and sold by brokers without your knowledge, requires a different strategy. That data often needs the persistent effort of a professional data removal service to find and eliminate.
The Invisible Threat: Understanding the Data Broker Industry
While you browse, shop, and live your life online, a hidden industry operates in the shadows. Data brokers are companies that collect your personal information, package it, and sell it to the highest bidder. This isn't a small-time operation; it's a massive, multi-billion dollar market. The global data brokerage market was valued at over $250 billion in 2024 and continues to grow with minimal oversight, turning your privacy into their profit.
These companies are relentless data collectors. They pull information from a vast network of sources, including:
Public Records: Your name, address, and political affiliation from voter registration files. Property records, marriage licenses, and court documents are also fair game.
Commercial Sources: Every time you use a retail loyalty card, your purchase history is logged and often sold. Your web browsing habits, location data from apps, and even your online search history are tracked and packaged.
Social Media: Public profiles on platforms like LinkedIn, Facebook, and Instagram are scraped for details about your career, relationships, and personal interests.
This aggregated data creates a direct pipeline for criminals and malicious actors. The connection between data brokers and the rise in cybercrime is undeniable. The FBI’s Internet Crime Complaint Center (IC3) received over 800,000 complaints in 2024, with phishing and identity theft among the top reported crimes. Scammers purchase lists from data brokers to craft highly personalized and convincing phishing emails, while doxxers buy home addresses to intimidate and harass their targets. Your exposed information becomes their primary weapon.
You may have tried removing your information from a people-search site, only to see it reappear weeks later. This happens because data brokers constantly trade, buy, and resell data among themselves. Deleting your profile from one site does nothing to stop dozens of others from repopulating it from their own sources. It’s a persistent cycle designed to keep your data in circulation.
How Your Data Is Monetized
Data brokers use a process called "data enrichment," where they combine disparate pieces of your information-your online activity, public records, and purchase history-into a single, comprehensive profile. This detailed dossier is then sold to insurance companies for risk assessment, predatory lenders to target vulnerable consumers, and advertisers for micro-targeted campaigns. As of 2026, the U.S. still lacks a singular, powerful federal law to regulate this industry, leaving consumers with few protections.
The Consequences of Exposure
The risks are not just digital. In 2025, a physician in California faced targeted harassment at her home after her address, sourced from a data broker, was posted on an extremist forum. Beyond physical safety, these profiles create a "digital reputation" that can influence your creditworthiness and insurance premiums. The constant awareness that your private life is a public commodity for sale creates a significant psychological burden, eroding your sense of security and autonomy.
Understanding this industry is the first critical step in learning how to protect your privacy online. Your personal information is a valuable asset, and it's time to regain control over who has access to it.
The Privacy Audit: A Step-by-Step Removal Framework
Taking control of your personal data begins with a thorough audit. You cannot protect what you don't know is exposed. This systematic process reveals your digital footprint, identifying precisely where your information is being collected, sold, and displayed online. It’s the foundational step in learning how to protect your privacy online and reclaim your digital identity from the data broker industry.
Identifying Your Privacy Gaps
A comprehensive personal data audit requires methodical searching. It’s more than a simple Google search of your name. Follow these steps to uncover where your most sensitive information lives:
Perform Targeted Searches: Use multiple search engines (Google, Bing, DuckDuckGo) to search for your full name in quotation marks, like "Jane Doe". Then, combine your name with current and past city names, phone numbers, and email addresses.
Prioritize High-Risk Data: Focus first on removing listings that expose your home address, phone number, date of birth, and the names of your family members. This is the Personally Identifiable Information (PII) most often used for doxxing, identity theft, and physical threats.
Scan the Dark Web: Use a trusted service like Have I Been Pwned to check if your email addresses or passwords have been compromised in known data breaches. A leaked password from a 2016 breach can still grant access to your accounts today.
Once you’ve identified the exposed data, the next phase is removal. This can be done manually through data broker opt-out pages, search engine removal tools like Google’s “Results about you,” or by formally requesting deletion under privacy laws like the California Consumer Privacy Act (CCPA) and Europe’s General Data Protection Regulation (GDPR). While these tools offer a path, the journey is intentionally difficult.
The Challenges of DIY Data Removal
The data removal process is a frustrating maze. Data brokers have no financial incentive to make it easy for you to opt out. Privacy experts estimate that a comprehensive manual cleanup can take over 100 hours of work, followed by ongoing maintenance. The core problem is that information reappears. After a successful removal, a broker may re-acquire your data from another source and republish your profile within 60 days. This creates a "whack-a-mole" issue that demands constant vigilance.
Brokers also use tactics designed to discourage you. Many require you to submit a copy of your government-issued ID to "verify" your identity, a practice that forces you to hand over more sensitive data. Others use confusing forms, hidden opt-out links, and multi-step confirmation processes that are easy to abandon. This system is not broken; it's working exactly as they designed it. For those serious about how to protect your privacy online, understanding these obstacles is critical. The manual process is built to be overwhelming. For a systematic and continuous solution, let deleteme experts handle the entire removal process for you.
Automating Your Privacy with deleteme
You've adjusted your browser settings, secured your social media, and use a VPN. Yet, your personal data remains exposed and for sale on the open market. Manually removing your information from hundreds of data broker sites is an overwhelming, often futile task. Each broker has a unique, intentionally complex opt-out process. For busy individuals in 2026, a professional data removal service is not a luxury; it's a logical necessity. This is the most effective step in learning how to protect your privacy online from the ground up.
deleteme provides a systematic solution to this problem. We combine proprietary AI scanning technology with a team of human privacy experts. Our automated systems continuously scan over 750 data broker sites for your personally identifiable information (PII), but automation alone isn't enough. When a broker uses deceptive designs or complex legal hurdles to prevent removal, our experts intervene directly to enforce your privacy rights. This hybrid approach ensures comprehensive and persistent removal where purely automated services fail.
Your privacy isn't a one-time task. It requires constant vigilance. Data brokers constantly scrape public records and online sources, meaning your information can reappear just weeks after a manual deletion. deleteme is built on the principle of continuous monitoring. We don't just remove your data once; we ensure it stays gone. This is verified through our commitment to total transparency. You receive regular, easy-to-read privacy reports that detail exactly which profiles were found and successfully removed, giving you tangible proof of your reduced digital footprint.
The deleteme Removal Process
Our service begins by systematically identifying your data profiles across our vast network of data broker and people-search sites. Once located, our dedicated privacy experts navigate the intricate web of legal opt-out requirements on your behalf. They handle the forms, the emails, and the verification steps designed to make you give up. Within your first 90 days, you can expect to see a dramatic reduction in your public online exposure, all documented in your first detailed privacy report.
Ongoing Vigilance and Peace of Mind
Data brokers frequently repopulate their databases, causing your removed information to "respawn." Our platform actively prevents this through automated rescans every three months, ensuring your shield remains active. For those with heightened security needs, we offer specialized protection plans for families and high-risk corporate executives who are frequent targets of doxxing and identity fraud. This relentless vigilance is the key to genuine peace of mind in a world of constant data collection.
Take control of your data today with deleteme.
Your 2026 Privacy Strategy Starts Now
In 2026, standard security tools aren't enough to shield your personal information. The real strategy for how to protect your privacy online involves actively removing your data from the hundreds of data broker sites that sell it. This is a continuous battle, as your information is constantly being re-added to these databases.
You don't have to fight this battle alone. Many resources and services exist that can help you reclaim your privacy. These solutions are designed to systematically find and remove your personally identifiable information from data broker sites, helping to mitigate your digital exposure. Utilizing such expert assistance can provide peace of mind and tangible results in data removal efforts.
It's time to erase your exposed data and restore your peace of mind. Taking proactive steps to remove your information can empower you to regain control over your digital identity. Your privacy is paramount, and your digital identity is yours to control.
Frequently Asked Questions
Is it actually possible to be 100% private online?
No, achieving 100% privacy online is practically impossible in our interconnected world. Daily activities like using social media, shopping, or even browsing leave a digital trail. The goal isn't total anonymity, which is unrealistic. Instead, the focus should be on significantly reducing your public exposure and taking control of your personally identifiable information (PII). This proactive approach minimizes your risk from data brokers and other online threats, giving you back control and peace of mind.
How do data brokers get my information in the first place?
Data brokers acquire your information from a vast network of public and private sources. They systematically scrape public records like property deeds, court filings, and voter registrations. They also purchase data from companies you do business with, such as retailers who sell your purchase history, or from apps that track your location. A 2022 Duke University study revealed some brokers purchase sensitive location data for as little as $0.25 per user, compiling detailed profiles without your direct consent.
Does using a VPN protect my privacy from data brokers?
A VPN only protects your privacy from data brokers in a limited capacity by masking your IP address. It encrypts your internet connection, preventing your Internet Service Provider (ISP) from seeing your activity. However, it doesn't stop data brokers from collecting information you provide elsewhere, like on social media or through public records. A VPN is one tool in your privacy arsenal, but it won't stop brokers from finding and selling data profiles they have already built on you.
How long does it take to remove my information from the internet?
The initial removal process can take anywhere from two to six weeks, but ongoing protection is required. Each data broker has a different opt-out procedure, with processing times ranging from 48 hours to over 45 days. The real challenge is that brokers often repopulate old data. This is why continuous monitoring and repeated removals are essential for long-term privacy. A comprehensive service ensures your information stays gone by regularly re-scanning and submitting new opt-out requests on your behalf.
What is the difference between a dark web scan and data broker removal?
A dark web scan alerts you to compromised credentials, while data broker removal actively deletes your public profiles. Dark web scans search for your email or passwords in known data breaches, telling you if your login information has been stolen. Data broker removal is a proactive service that finds and scrubs your personal profiles from sites that legally collect and sell your data. One is a reactive alert system; the other is a protective measure to reduce your public footprint and prevent future misuse.
Can I remove my personal information from Google search results?
Yes, you can request the removal of specific personal information from Google search results, but this action doesn't delete the source. Google's "Results about you" tool, updated in 2023, lets you request the de-indexing of search results containing your address or phone number. However, this only removes the link from Google. The information still exists on the original website. To truly protect your privacy online, you must remove the data from the source first to prevent it from being re-indexed.
Is a paid privacy service like deleteme worth the investment?
Yes, a paid service is worth the investment for anyone who values their time and wants comprehensive, continuous protection. Manually opting out of hundreds of data broker sites is a complex and time-consuming process that requires ongoing maintenance. A service like deleteme automates this, with privacy experts handling the entire removal and verification process for you. For a subscription fee often less than $11 per month, you gain peace of mind and expert-led vigilance that saves you dozens of hours per year.
What should I do if my information reappears after I delete it?
If your information reappears, you must resubmit the removal request to the data broker. Data brokers constantly update their databases and may re-add your profile from a new source. This is the primary reason manual removal is often ineffective long-term. A dedicated privacy service resolves this by performing regular scans, typically every 3-4 months. When your data is found again, the service automatically handles th
Need help? Visit our Help Center.
More Privacy Tips





